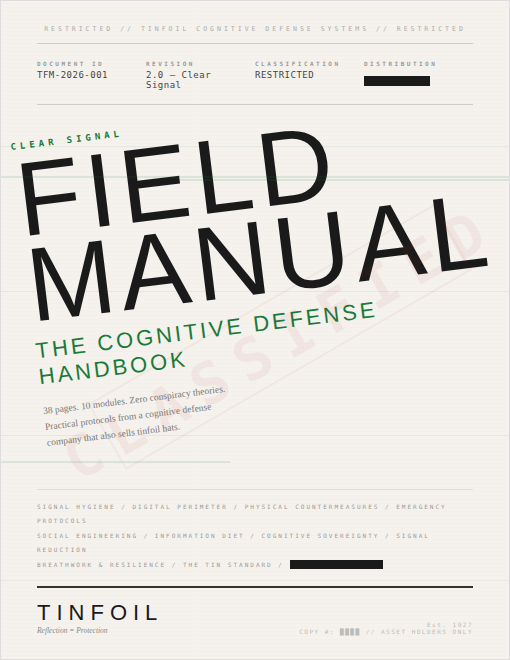
CLASSIFICATION: RESTRICTED — DIGITAL DISTRIBUTION AUTHORIZED – FORMAT: Digital PDF // Instant deployment // 38 pages
Your phone transmits your behavioral data to between 15 and 40 companies every single day. Your apps are listening. Your browser is profiling you. Your attention has been auctioned to the highest bidder. And your nervous system has been quietly rewired by notification patterns designed by people who studied B.F. Skinner in college.
None of this is a conspiracy theory. It’s a business model you agreed to without reading the terms of service.
The Field Manual is the counter-operation.
What’s Inside
38 pages. 10 modules. Practical protocols you can implement immediately.
Written by a cognitive defense company that also sells tinfoil hats — this handbook contains actionable security advice that would cost $300/hour from a cybersecurity consultant, combined with mental resilience techniques used by special forces combat operations and Olympic-level athletes. Some of it is genuinely life-changing. Some of it is mildly paranoid. All of it is more interesting than whatever your algorithm was about to show you next.
MODULE 00 — THREAT ASSESSMENTUnderstand your actual adversaries. Not the ones you imagine — the ones documented in peer-reviewed research. The five adversary tiers from opportunistic criminals to state-level actors, plus a personal threat matrix that tells you exactly where you’re exposed.
MODULE 01 — SIGNAL HYGIENE The 10-minute permissions audit that reduces your passive data emissions by 60–80%. The app purge. The notification discipline protocol. The advertising ID reset. Four steps. Thirty minutes. Dramatically less surveillance.
MODULE 02 — DIGITAL PERIMETERPasswords, browsers, VPNs, encrypted messaging, email security. The boring stuff that actually saves your life — explained without jargon and with honest assessments of what works and what’s theater.
MODULE 03 — PHYSICAL COUNTERMEASURES Faraday bags, RFID shielding, webcam covers, and the real physics of electromagnetic shielding. Because some threats exist in the physical world.
MODULE 04 — EMERGENCY PROTOCOLS DIY Faraday shielding (yes, it works — with caveats). The microwave oven test. Clean device procedures. And the operational communications protocol that Hollywood gets wrong.
MODULE 05 — SOCIAL ENGINEERINGPhishing, pretexting, baiting, tailgating — the oldest hacks in the world don’t require a computer. Plus the social media OPSEC checklist that reveals how much of your life is already public.
MODULE 06 — INFORMATION DIET How algorithms actually work. Why your feed is 80–90% curated content you didn’t choose. The 24-hour rule. The module that separates TINFOIL from every other privacy brand.
MODULE 07 — COGNITIVE SOVEREIGNTY ★ The module nobody expects from a privacy guide. Breathwork protocols from Navy SEALs (box breathing), the Wim Hof method (laboratory-validated), Rickson Gracie’s diaphragmatic technique (combat-tested), intentional discomfort training, and a daily field protocol for maintaining cognitive readiness. This module protects your mind — not just your data.
MODULE 08 — THE TIN STANDARD Self-assessment certification from Level 1 (Curious) to Level 5 (DEFCON Protocol). Track your progress. Know your readiness level.
MODULE 09 — SIGNAL REDUCTION How visible you actually are — and which levers you can pull. Every system that currently knows your location mapped in one place, data broker opt-out protocols, physical visibility reduction for transactions and movement, and the honest truth about “going off the grid.” Plus a classified teaser for Underground members who want the complete disappearance framework.
Plus: Field Communication Standards (recognition protocols for identifying fellow assets), Quick Reference Cards, Data Broker Opt-Out Checklist, Recommended Tools, and Field Notes pages.
Who This Is For
- You checked your phone 4 times while reading this product description
- You reuse passwords and know you shouldn’t
- You’ve thought “my phone is definitely listening to me” at least once
- You want practical security advice without the tech-bro gatekeeping
- You believe your attention is worth protecting
- You bought a hat and want to know what else you can do
What This Is Not
This is not a conspiracy theory manual. There are zero mentions of lizard people, flat earth, or chemtrails. This is documented facts, peer-reviewed research, and practical protocols. If anything, the real information is more unsettling than the conspiracy theories.
Format
📥 Digital download — PDF delivered instantly after purchase
- 38 pages — designed for screen reading and optimized for printing & emergency resource
- Minimal ink consumption — print it without bankrupting your toner budget
- Includes printable spine template for physical binding
The Fine Print
Nothing in this document constitutes legal, medical, electromagnetic engineering, or spiritual advice. We are a cognitive defense company. A very suspicious cognitive defense company. But a cognitive defense company nonetheless.
REFLECTION = PROTECTION